TL;DR
Cisco AnyConnect VPN software fails to connect with the error “Hostscan is waiting for the next scan” when there are too many certificates in your Personal Certificates folder. Fiddler creates a LOT of certificates when you allow it to intercept HTTPS traffic. Clearing these certificates will resolve this error. Jump to The Solution or read on for details…
The Scenario
I use Fiddler on a daily basis to redirect requests for external web resources back to my local machine. This saves a huge amount of time by allowing me to simply build (transpile) locally without having to upload the changed files after every edit. This is a big deal when writing custom code inside the Microsoft Dynamics CRM ecosystem. There are plenty of postings about this technique, but here’s short one that gets right to the point.
I also use Cisco AnyConnect VPN to connect to the network of my client. This is a pretty common scenario for many remote workers.
The Problem
Several days after starting work for this client, I experienced a problem when I attempted to connect to the VPN one morning. Rather than connecting and prompting me for my credentials, the AnyConnect client showed me this message:
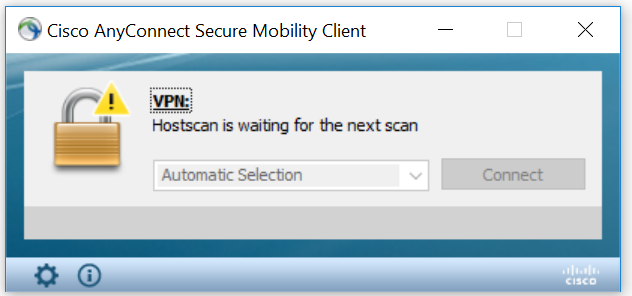
This message stayed around without changing and without any other sign of activity. Eventually, it timed out and the VPN connection failed. Several more attempts yielded the same result.
A quick search turned up a fantastic explanation of the problem by Matt LaPaglia. The short explanation is that allowing Fiddler to capture HTTPS traffic results in creating a fake Certificate for each website that it intercepts. This is effectively a legitimate use of the Man-in-the-middle attack technique. The number of certificates can become quite large after using Fiddler for a while, depending on how many different websites you visit. Here’s what my Personal Certificates folder looked like after using Fiddler for a few days:

Notice the “DO_NOT_TRUST_FiddlerRoot” issuer in the “Issued By” column. Those were all created by Fiddler. You can see your own Certificates by running certmgr.msc and navigating to Personal | Certificates.
As it turns out, the warning message from Cisco AnyConnect is actually displayed every time you connect to VPN. But usually it comes and goes very quickly so that you don’t notice it. AnyConnect always scans your Personal Certificates before allowing you to connect – probably looking for known bad ones.
But when it’s faced with dozens and dozens of certificates to scan, it times out.
The Solution
The solution proposed by Matt LaPaglia works. He recommends manually deleting all of the “DO_NOT_TRUST_FiddlerRoot” certificates. I tried that the first time and it definitely worked. The very next time I attempted to connect to VPN it went through almost immediately.
There are some small issues with Matt’s solution. First, there’s the possibility that you might mistakenly delete a real certificate that you need to keep, such as one issued by your enterprise or another developer. Second, it takes manual effort and I’m lazy efficient.
However, there’s a better way. I’m not familair with the timing of when this feature was introduced – perhaps this wasn’t available when Matt wrote his article. I’m currently using Fiddler v5.0.20182 (built June 27, 2018).
Inside Fiddler, there’s a command that will automatically clear these certificates for you. Here are the steps:
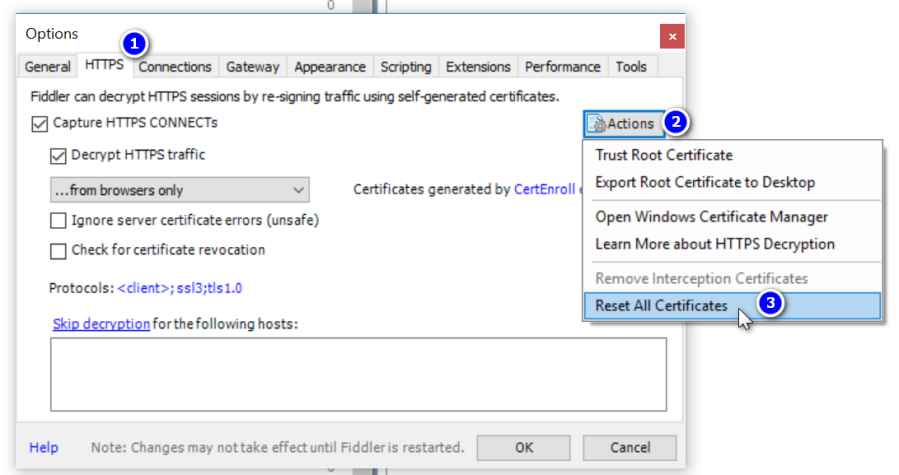
- In Fiddler, navigate to Tools | Options and select the HTTPS tab.
- Click the “Actions” button
- Select “Reset All Certificates”
- Click OK and Yes to quite a few prompts that follow. Fiddler will ask for your permission to remove the current certificates and show standard Windows security warnings and UAC prompts in order to allow it to reinstall the new Fiddler root certificate. (Note: You’ll need to have local administrator access in order to complete this!)
After performing this reset, there should only be ONE certificate left from Fiddler (although it won’t stay this way for long). And Cisco AnyConnect VPN should connect as fast as a speeding jet plane (or 4), at least until the certificates accumulate enough to need clearing again.

What’s Fiddler exactly?
LikeLike
Fiddler (https://www.telerik.com/fiddler) is a free tool from Telerik that intercepts all of your network traffic. This is most useful for web developers by allowing you to analyze and debug the behavior of your page, site, or service. It also allows you to redirect or modify traffic. In the case of developing custom scripts for Microsoft Dynamics 365 I’m able to make my browser consume script files from a local path rather than having to constantly deploy them during the development process.
LikeLike
Well done. Worked like a charm.
LikeLike
Hi John, thanks for taking time to comment. Glad this solution helped you – I used it myself just this week!
LikeLike
Thank you Mark,
saved my day !
LikeLiked by 1 person
Thanks for your comment, Maxime. So glad this helped!
LikeLike
Thank you Mark,
saved my day
LikeLiked by 1 person
Glad it helped, Khaon!
LikeLike
Thanks a lot, Mark. This even fixed slow VPN issues for me.
LikeLiked by 1 person
Thanks for your comment, @iamtechtips. Glad this helped!
LikeLike
Wow this really saved my bacon – had my IT team baffled for about a week as to why this was happening!! It really works! Thanks again!
LikeLike
Hi Tom – thanks so much for taking time to comment. Glad this helped!
-Mark
LikeLike
Cool Solution. It helped, Atleast the frequency to connect is improved. There is still a single certificate Do_Not_Trust_FiddlerRoot in TrustedRootCertificationAuthorities should this be deleted as well.
LikeLike